Cybercrime is ever present, and there is one particular fraud we all should be aware of—particularly anyone who sends or receives bank wiring instructions or the funds themselves. The fraud involves the hacking or impersonating of email accounts, it might be called business email compromise (BEC) fraud, CEO fraud, or CFO fraud, and it demonstrates that criminal participants are infinitely adaptable in pursuit of profitable schemes. Cybercrime is not always a technical attack, but often about social engineering—tricking a person into performing an action—which means we need to stay informed, be alert, and exercise sound judgment.
Email schemes and bank wiring frauds
First, let’s review how things are supposed to work when we send a bank wire. We want to send money from our bank account to theirs, the recipient tells us where we should wire the funds, we relay those instructions to the bank, and the bank sends the money from our account to the beneficiary’s account.
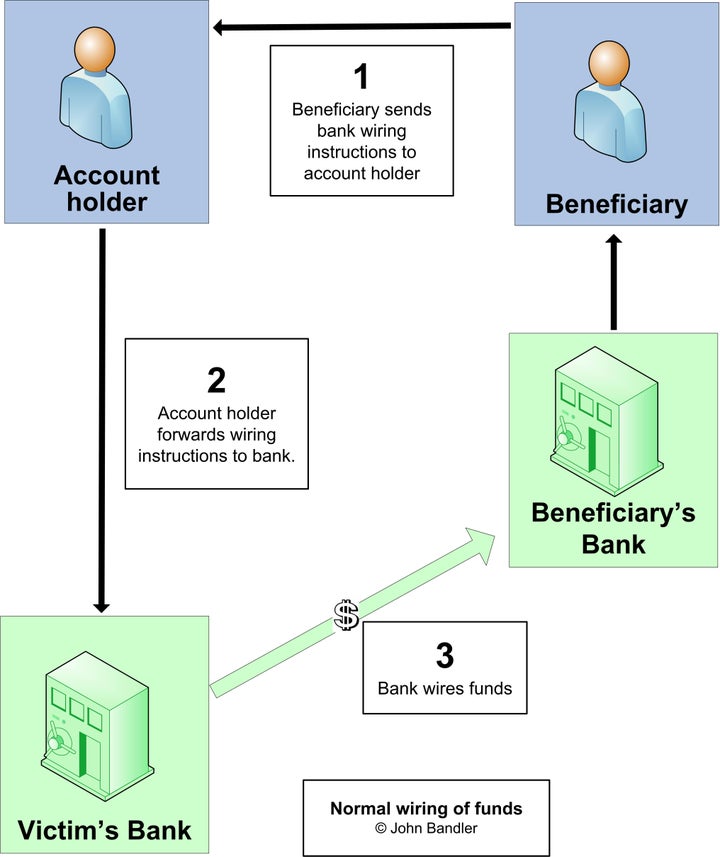
Normal wiring of funds
When cybercrime was a newer industry, cybercriminals attacked banks who then learned to protect themselves. Then cybercriminals realized that the account holder was an easier point of compromise, with less security than the bank. By compromising the account holder’s financial account credentials, or email account credentials, they could impersonate the account holder, direct the bank to send a wire to an account controlled by the criminal, and then forward the funds out of the country. This was done without the consent or knowledge of the account holder, and is depicted like this.
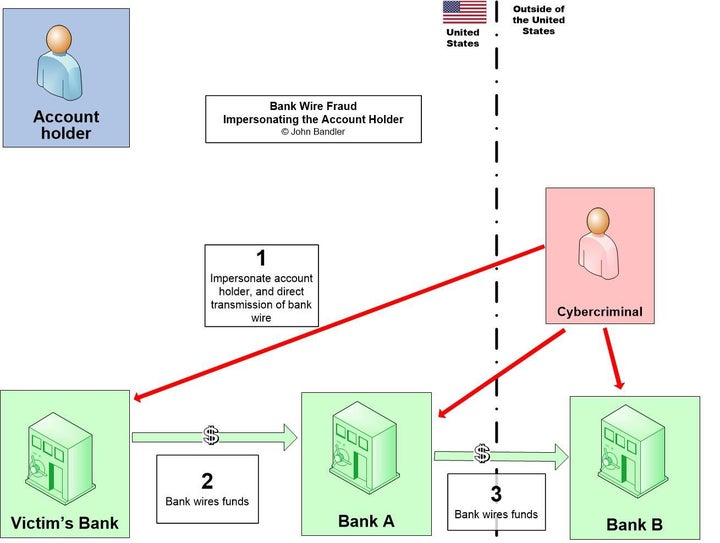
Bank Wire Fraud - Impersonating the Account Holder
When this scheme is successful the criminals get away scot-free with the money, and then it is between the account holder and bank to figure out who should bear the loss. Sometimes fault is not clear, but if the account holder was negligent in allowing their internet account or computer to be hacked, perhaps they should bear some or all of the loss. If the bank was tricked by a criminal, and wired customer funds without the consent of the account holder, then perhaps the bank should bear the entire loss. The result was that banks became wise to this fraud and implemented controls to reduce it, taking steps to confirm that the wiring instructions are being sent by the account holder—and not by a fraudster. These measures include a verbal conversation and confirmation of bank wiring instructions. While anti-fraud measures are good business practices and protect against monetary loss, banks also have legal and regulatory obligations to prevent and report fraud and money laundering activity, and are in an excellent position to identify and respond to new fraud trends.
With these improved controls it became harder for cybercriminals to commit that specific fraud so they evolved. Instead of impersonating the account holder and tricking the bank, they impersonate the person who sends the account holder the bank wiring instructions—tricking the account holder. Unlike the bank, the account holder probably has no training in anti-fraud and anti-money laundering, and may not know about the need to verify that wiring instructions are authentic. The account holder receives fraudulent instructions and simply forwards them to the bank. The bank receives these instructions from the account holder, and verifies that the instructions were in fact sent from the account holder, but perhaps does nothing to advise the account holder about this new fraud scheme. The bank executes the customer’s instructions, the money is wired, and thus stolen, as shown below.
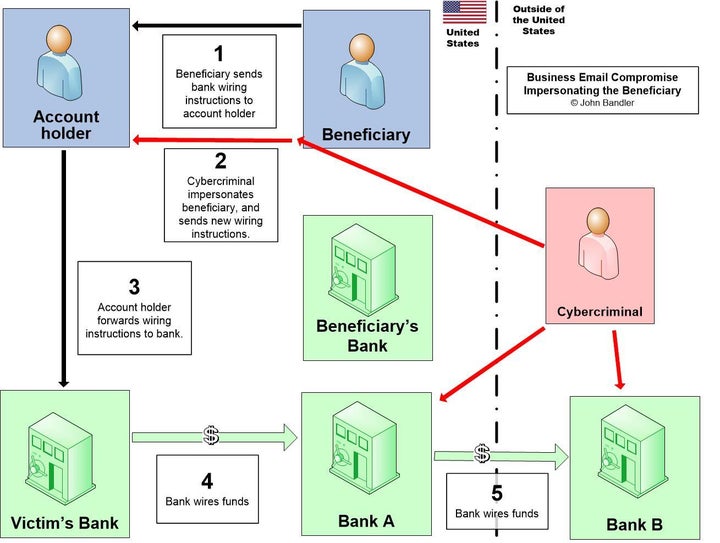
Impersonating the Beneficiary
This fraud is rampant, and many banks take the position that this is solely the fault of the account holder, who must bear the entire theft loss, given that the bank merely did what the account holder instructed it to do. Some banks seem to expend minimal effort to recover the stolen funds, especially in the critical hours after the first wire transfer. However, it is the banks who are in the best position to move quickly, trace the funds, and stop them from moving further, especially before they are transferred out of the country. It is also the banks who are in the best position to identify money mule accounts, as the account in “Bank A” represents. Arguably, banks might act more aggressively to recover stolen funds if it were their funds to be recovered, rather than their customer’s funds, and there are probably instances where the bank may not be as blameless nor as diligent as it might lead the customer to believe.
The money mule
The cybercriminals committing this fraud don’t receive stolen funds directly, so they use one or more money mules—people recruited to receive a fraudulent bank wire or forged check—to receive and then forward the funds. The cybercrime economy is lucrative, so it is now very good at laundering money, and this is one way they do it.
Cybercriminals use a variety of techniques to recruit money mules to receive these fraudulent bank wires or forged checks. A fraudster tried to recruit me the other day with this email:
Hi, Can you help us in drafting a purchase ... agreement of oil rig equipment with a buyer in your state?
Regards,
[Impersonated victim’s name]
Had I responded, eventually they would have asked me to receive a check or a bank wire which would eventually be revealed as fraudulent. This solicitation wasn’t believable—especially since New York isn’t a big market for buyers of oil rig equipment—but others are more believable. It could be “work at home” business opportunities to help collect a debt, settlement, or purchase property. The unsuspecting money mule thinks he or she will earn a fee for this service, but will earn nothing, and may face civil liability for the entire amount of the fraudulent transaction. Money mules are needed for frauds of all sizes, from hundreds of dollars to millions of dollars.
Protect yourself
There’s a few things you need to do to protect yourself. They boil down to:
- Keep your financial and email accounts from being hacked.
- Verify that people you deal with haven’t had their accounts hacked.
- Confirm wiring instructions verbally.
- Don’t become a money mule. Know who you are dealing with, know their business, and know the source and destination of funds.
You can keep your email accounts and financial accounts from being hacked by using strong passwords that are changed periodically, and by enabling two factor authentication (two step login). Periodically review your privacy and security settings.
Ensure that you—and your company—always verbally confirm payment instructions that are sent to you from people inside or outside your organization. Businesses also need financial controls which include dual control and segregation of duties to prevent a single person from causing funds to be sent. Get to know the people and businesses that you work with and transfer funds with. If things seem suspicious, or change without adequate explanation and confirmation, or if names don’t match, that could indicate fraud or money laundering.
If you are a victim
If you are a victim of this crime, report it to the bank and to law enforcement immediately. Report to the FBI’s Internet Crime Complaint Center (IC3), report to the local police, and if the fraud amount is significant call the local FBI field office. See the FBI’s advisory on this fraud for more information.
Preserve all evidence of the crime, and document your communications with the bank and law enforcement. Of course, preserve all communications to and from the cybercriminals, and don’t delete those emails.
Consider hiring a professional to assist you. The bank’s interests are different from yours and they may not be as motivated to recover funds if they believe it is your money, rather than theirs. Banks might not be allowed to share certain information with you by law, and sometimes they might not share information if it might be ammunition in a lawsuit or regulatory action. Law enforcement might not investigate as thoroughly as you might like, and even when they do, their focus is pursuing a criminal investigation, and they might not be allowed to share certain information with you.
In order to effectively fight cybercrime, our country will need to develop seamless crime reporting methods, which are followed by a prompt and effective investigative response. We are not there yet, so persistence by the crime victim may be required. We should encourage government to comprehensively fight the cybercrime economy, which it is not yet doing. This fraud is one of many evolving frauds, so personal and business cybersecurity and anti-fraud measures are essential—we need to educate and protect ourselves.